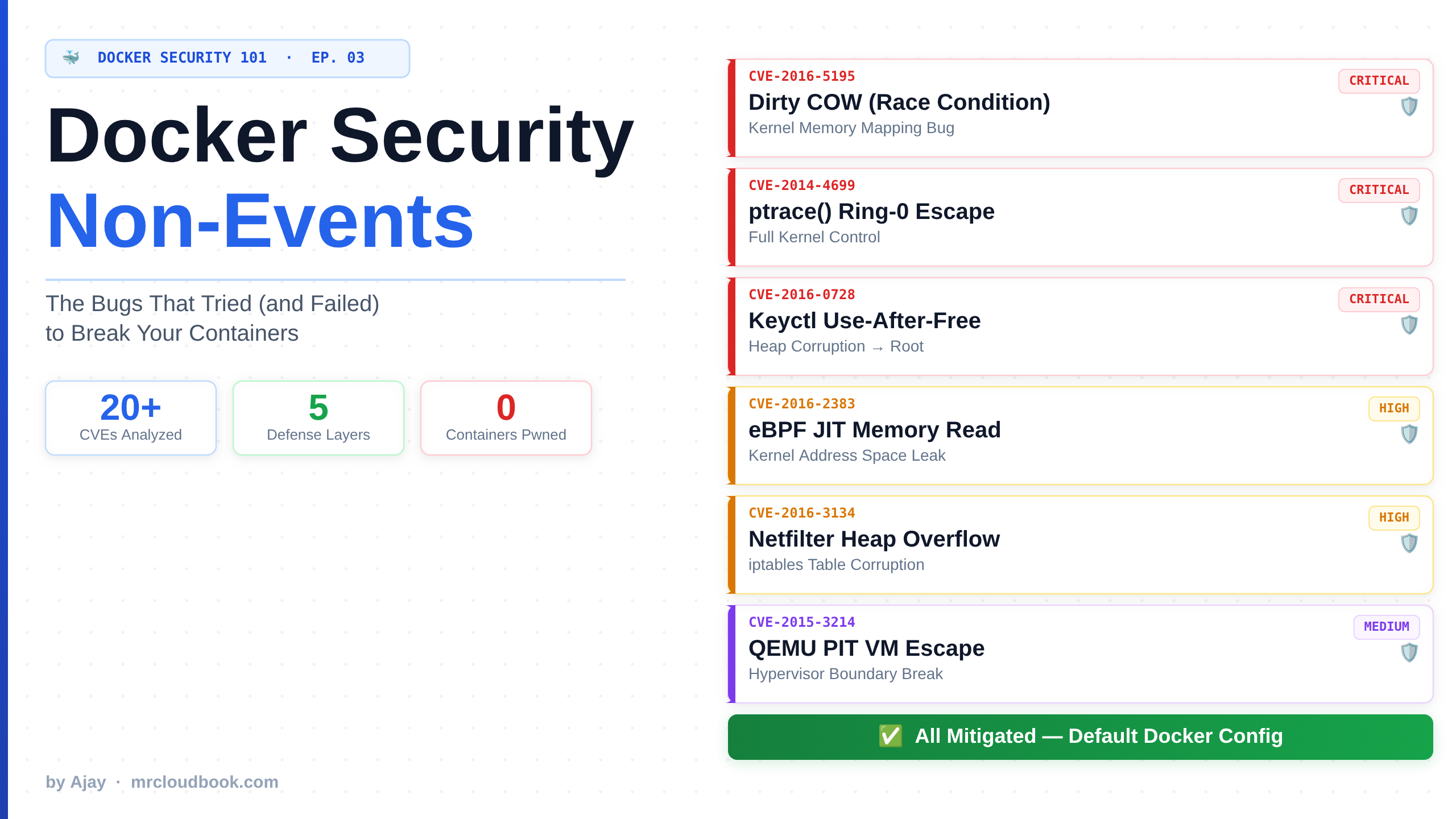
Docker Security: The Bugs That Tried to Ruin Your Day
Docker actually noticed to have attracted security review and publicly disclosed vulnerabilities. In all likelihood, the bugs that haven't been reported far outnumber those that …
Hands-on DevOps, Cloud, and Kubernetes tutorials - from setup to production.
Docker actually noticed to have attracted security review and publicly disclosed vulnerabilities. In all likelihood, the bugs that haven't been reported far outnumber those that …
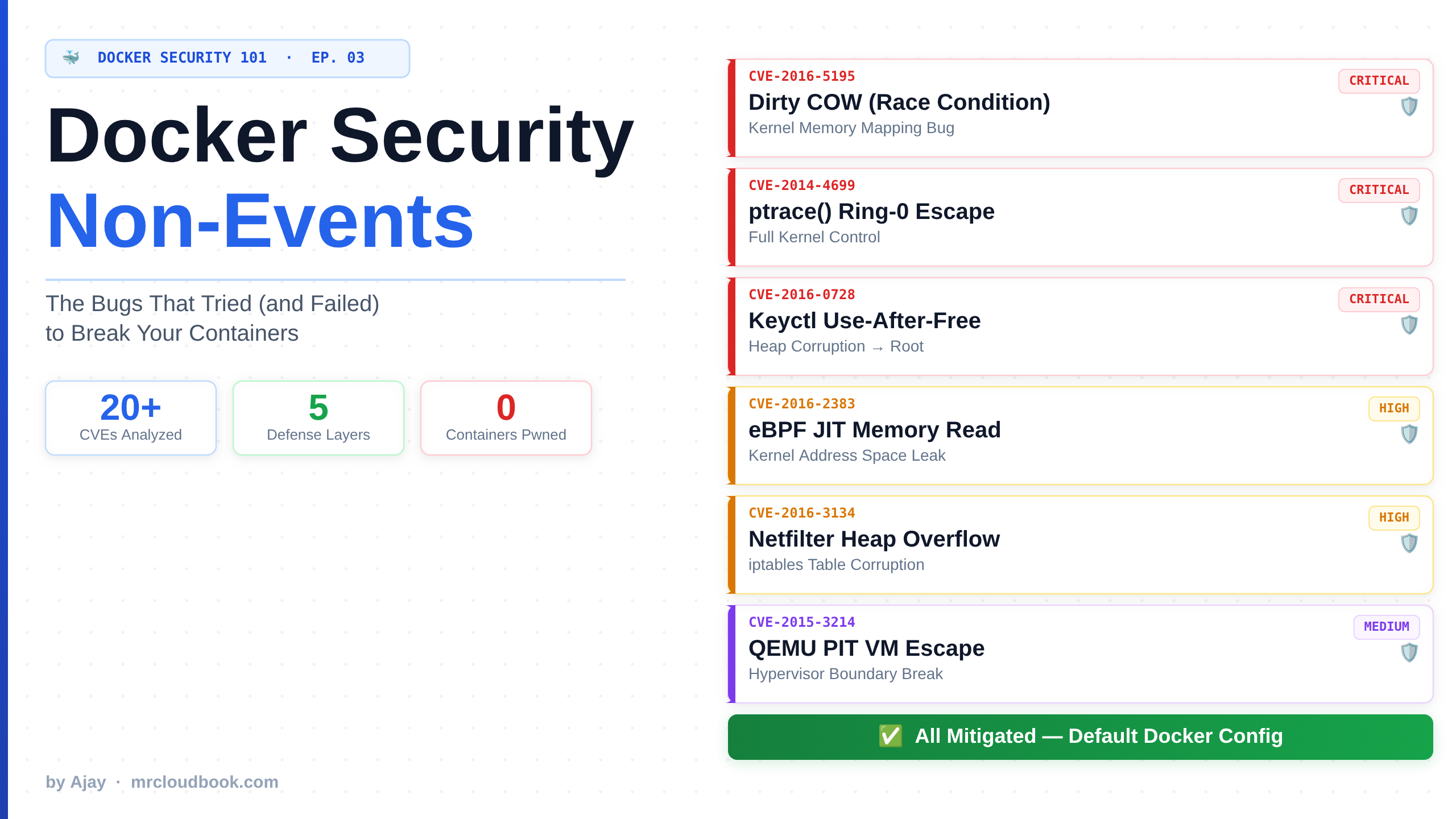
What is AppArmor?Let me be direct with you. I've been running containerized workloads in production for over 4 years. In that time, I've seen everything …

I've been running containers in production for 4 years, and I'll be real with you: Docker's default configuration is terrifyingly permissive. It's one of those …

Trivy Got Hacked: What Actually Happened?

Something’s eating CPU or memory, and you need to see exactly what — fast. If you’ve ever stared at top and wondered what half the …

How to use Hadolint to lint Dockerfiles, catch security issues and anti-patterns before build, fix common mistakes (version pinning, non-root users, exec-form CMD), and integrate …
The useradd command is one of the most fundamental tools for user management in Linux systems. It allows system administrators to create new user accounts, …

eBPF This blog breaks down "Learning eBPF" in simple terms, assuming you're completely new to programming and Linux concepts. Don't worry if you don't know …
Prologue: The VisionIn the vast digital landscape where countless applications struggle to find their voice, where developers battle with manual configurations, and where SSL certificates …